
1-click Experiment Setups
Infrastructure

Data and Data Repository

Your Security Is Our Priority





Công cụ DFIRtriage được viết bằng ngôn ngữ Python bởi tác giả Travis Foley có chức năng thu thập chứng cứ phục vụ mục đích điều tra trong lĩnh vực truy tìm manh mối chứng cứ số. Nó thực sự hữu ích cho hoạt động phản ứng sự cố dựa trên Windows.
DFIRtriage thu thập dữ liệu từ máy tính mà nó được thực thi. Do đó, để thu thập được thông tin từ các máy chủ từ xa, các tập tin của DFIRtriage sẽ cần được sao chép vào máy tính mục tiêu, sau đó được thực hiện thông qua shell từ xa. (ví dụ: SSH hoặc PSEXEC)
Tất cả những gì bạn cần để bắt đầu thu thập thông tin có giá trị là đặt 2 tập tin dfirtriage.exe và core.ir trong cùng một thư mục trên máy tính mục tiêu (máy tính cần tìm kiếm thông tin bằng chứng) và thực thi dfirtriage.exe với quyền quản trị viên.
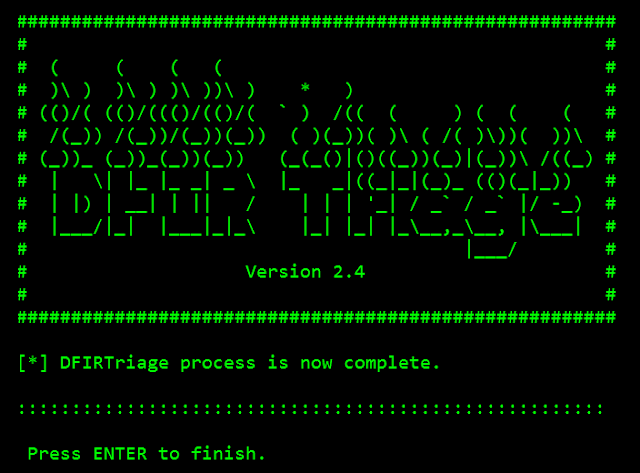
Liên kết tải công cụ: https://github.com/travisfoley/dfirtriage
Công cụ sẽ thực hiện thu thập được những thông tin như sau:
Tham khảo: Github
What is this?
What is this ?
What is this?
What is this ?
To access CyberTrain, researchers need to register for an account at the official website. The Account registration will sent to for verification. Once the profile is verified, researchers can start requesting data sets from CyberTrain.
Visit the website to create an account and browse the training datasets available. Contact us for any help you require.
Follow us: https://www.facebook.com/inseclab/